CVE-2026-33179
libfuse: NULL Pointer Dereference and Memory Leak in io_uring Queue Initialization
Description
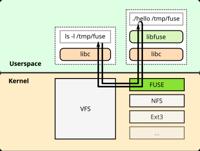
libfuse is the reference implementation of the Linux FUSE. From version 3.18.0 to before version 3.18.2, a NULL pointer dereference and memory leak in fuse_uring_init_queue allows a local user to crash the FUSE daemon or cause resource exhaustion. When numa_alloc_local fails during io_uring queue entry setup, the code proceeds with NULL pointers. When fuse_uring_register_queue fails, NUMA allocations are leaked and the function incorrectly returns success. Only the io_uring transport is affected; the traditional /dev/fuse path is not affected. PoC confirmed with AddressSanitizer/LeakSanitizer. This issue has been patched in version 3.18.2.
INFO
Published Date :
March 20, 2026, 9:17 p.m.
Last Modified :
March 27, 2026, 9:20 p.m.
Remotely Exploit :
No
Source :
[email protected]
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | MEDIUM | [email protected] |
Solution
- Update libfuse to version 3.18.2 or later.
- Ensure io_uring transport is configured securely.
- Monitor system for FUSE daemon stability.
Public PoC/Exploit Available at Github
CVE-2026-33179 has a 1 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2026-33179.
| URL | Resource |
|---|---|
| https://github.com/libfuse/libfuse/commit/7beb86c09b6ec5aab14dc25256ed8a5ad18554d7 | Patch |
| https://github.com/libfuse/libfuse/releases/tag/fuse-3.18.2 | Product Release Notes |
| https://github.com/libfuse/libfuse/security/advisories/GHSA-x669-v3mq-r358 | Vendor Advisory |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2026-33179 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2026-33179
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
RingWraith: CVE-2026-33150 and CVE-2026-33179 — Use-After-Free and NULL Dereference in libfuse io_uring
Shell Ruby HTML C Java Python
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2026-33179 vulnerability anywhere in the article.

-
Daily CyberSecurity
The MuPDF Vulnerability Turning “Safe” PDFs into System Hijackers
A significant security flaw has been unearthed in Artifex MuPDF, a popular framework prized for its speed and versatility in handling PDFs, XPS, and e-books. Labeled as CVE-2026-3308, this integer ove ... Read more
-
Daily CyberSecurity
Critical libfuse io_uring Vulnerabilities Threaten Linux and Kubernetes Infrastructure
The FUSE (Filesystem in Userspace) project, a staple of the Linux ecosystem that allows non-privileged users to create their own file systems, is facing a dual-threat. Researchers have identified two ... Read more
The following table lists the changes that have been made to the
CVE-2026-33179 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Initial Analysis by [email protected]
Mar. 27, 2026
Action Type Old Value New Value Added CPE Configuration OR *cpe:2.3:a:libfuse_project:libfuse:*:*:*:*:*:*:*:* versions from (including) 3.18.0 up to (excluding) 3.18.2 Added Reference Type GitHub, Inc.: https://github.com/libfuse/libfuse/commit/7beb86c09b6ec5aab14dc25256ed8a5ad18554d7 Types: Patch Added Reference Type GitHub, Inc.: https://github.com/libfuse/libfuse/releases/tag/fuse-3.18.2 Types: Product, Release Notes Added Reference Type GitHub, Inc.: https://github.com/libfuse/libfuse/security/advisories/GHSA-x669-v3mq-r358 Types: Vendor Advisory -
New CVE Received by [email protected]
Mar. 20, 2026
Action Type Old Value New Value Added Description libfuse is the reference implementation of the Linux FUSE. From version 3.18.0 to before version 3.18.2, a NULL pointer dereference and memory leak in fuse_uring_init_queue allows a local user to crash the FUSE daemon or cause resource exhaustion. When numa_alloc_local fails during io_uring queue entry setup, the code proceeds with NULL pointers. When fuse_uring_register_queue fails, NUMA allocations are leaked and the function incorrectly returns success. Only the io_uring transport is affected; the traditional /dev/fuse path is not affected. PoC confirmed with AddressSanitizer/LeakSanitizer. This issue has been patched in version 3.18.2. Added CVSS V3.1 AV:L/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H Added CWE CWE-476 Added Reference https://github.com/libfuse/libfuse/commit/7beb86c09b6ec5aab14dc25256ed8a5ad18554d7 Added Reference https://github.com/libfuse/libfuse/releases/tag/fuse-3.18.2 Added Reference https://github.com/libfuse/libfuse/security/advisories/GHSA-x669-v3mq-r358